Frequently Asked Questions
Product Information
What is FalkorDB and how does it support cybersecurity?
FalkorDB is a high-performance, open-source graph database designed for cybersecurity applications. It enables organizations to model, store, and analyze interconnected security data—such as IP addresses, domains, users, and attack patterns—using a native graph structure. This approach supports advanced Cypher querying, real-time detection, and context-rich investigations for use cases like CNAPP, CSPM, CIEM, IAM, and more. [Source]
What types of cybersecurity solutions is FalkorDB ideal for?
FalkorDB is ideal for CNAPP (Cloud-Native Application Protection Platform), CSPM (Cloud Security Posture Management), CIEM (Cloud Infrastructure Entitlement Management), DAST (Dynamic Application Security Testing), SAST (Static Application Security Testing), and IAM (Identity and Access Management) solutions. Its graph-native approach enables advanced threat modeling, real-time detection, and multi-tenant data isolation for these use cases. [Source]
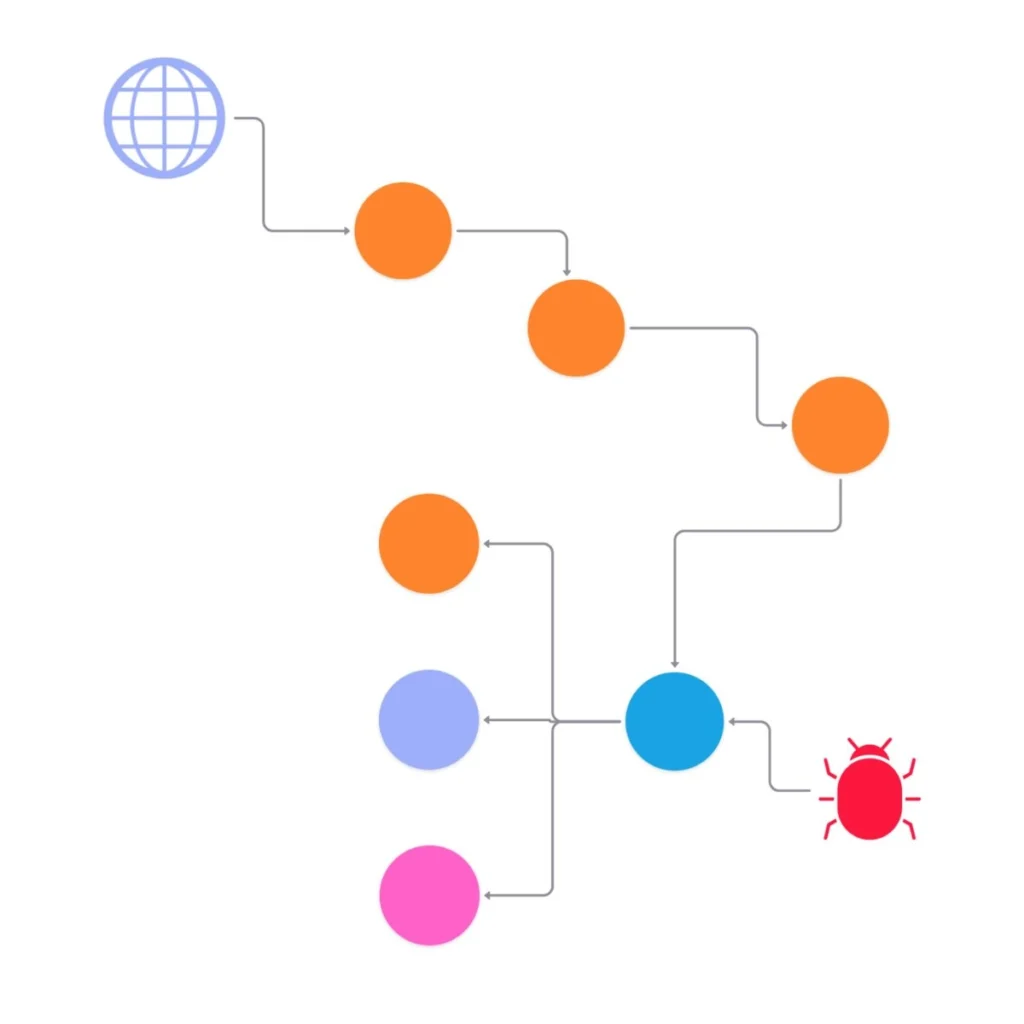
How does FalkorDB model cybersecurity data?
FalkorDB models cybersecurity data as a graph, preserving the natural relationships between entities such as users, systems, IP addresses, and vulnerabilities. This allows for flexible schema evolution and advanced Cypher queries, making it easier to correlate threats and uncover attack paths as security requirements change. [Source]
What is the primary purpose of FalkorDB in cybersecurity?
The primary purpose of FalkorDB in cybersecurity is to provide a scalable, multi-tenant, and ultra-fast graph database that enables real-time detection, advanced threat modeling, and efficient management of complex security data. It helps organizations move from reactive firefighting to proactive prevention by delivering faster investigations and smarter risk prioritization. [Source]
What are the core problems FalkorDB solves for cybersecurity teams?
FalkorDB addresses challenges such as alert fatigue, lack of context in threat detection, slow investigations, and rigid data schemas. By enabling end-to-end context resolution and real-time multi-hop graph queries, FalkorDB helps security teams prioritize incidents, reduce false positives, and build higher-fidelity threat models. [Source]
How does FalkorDB enable real-time detection in cybersecurity?
FalkorDB processes multi-hop graph queries in milliseconds, enabling real-time insights and detection of threats as they emerge. This ultra-low latency is critical for identifying and responding to attacks before they escalate. [Source]
What is the advantage of using a graph database for security data?
Security data is inherently interconnected, with relationships between users, systems, vulnerabilities, and attack vectors. Graph databases like FalkorDB preserve these relationships natively, support flexible schemas, and enable advanced querying—making it easier to correlate threats, prioritize risks, and adapt to evolving security landscapes. [Source]
How does FalkorDB support multi-tenancy for cybersecurity applications?
FalkorDB offers built-in multi-tenancy, supporting over 10,000 tenants with fully isolated data. This allows SaaS providers and enterprises to manage diverse user bases efficiently, with zero wasted infrastructure and seamless scalability for future workloads. [Source]
What query language does FalkorDB support for security analytics?
FalkorDB supports the Cypher query language, which is widely used for graph analytics and enables advanced querying of interconnected security data. This allows security analysts to perform complex investigations and threat modeling with ease. [Source]
How does FalkorDB improve the user experience for security teams?
FalkorDB delivers a frictionless user experience by enabling interactive dashboards, data filtering, and custom views. This empowers security teams to explore complex data visually, accelerate investigations, and make informed decisions quickly. [Source]
How does FalkorDB help with alert fatigue and incident prioritization?
FalkorDB enables end-to-end context resolution, allowing security teams to correlate alerts, prioritize incidents, and focus on the most critical threats. This reduces false positives and analyst burnout, leading to more effective threat response. [Source]
What business impact can organizations expect from using FalkorDB for cybersecurity?
Organizations using FalkorDB can expect faster investigations, smarter risk prioritization, fewer false positives, and a simpler path to securing complex cloud infrastructures. By leveraging graph-native analytics, teams can fix the most important incidents first and improve overall security posture. [Source]
How does FalkorDB handle schema evolution as security requirements change?
FalkorDB's graph-native approach supports flexible schema evolution, allowing organizations to adapt their data models as new threats and requirements emerge. This flexibility ensures that security analytics remain effective even as the threat landscape evolves. [Source]
Why is graph representation better than relational schemas for security data?
Graph representation preserves the interconnected nature of security data, making it easier to model relationships and adapt to changing threats. Relational schemas force data into rigid tables, which can hinder context resolution and slow down investigations. Graph databases like FalkorDB provide the flexibility and performance needed for modern security analytics. [Source]
How does FalkorDB help with securing complex cloud infrastructures?
FalkorDB structures and accelerates security data, enabling faster investigations, smarter risk prioritization, and more effective prevention strategies for complex cloud environments. Its multi-tenant, scalable architecture is designed to support the needs of modern cloud security teams. [Source]
What are the key features of FalkorDB for cybersecurity?
Key features include support for 10K+ multi-tenant graphs, real-time detection, Cypher query language, built-in multi-tenancy, ultra-fast query performance, and a frictionless user experience with dashboards and custom views. [Source]
How does FalkorDB enable smarter risk prioritization?
By correlating IAM misconfigurations, workload vulnerabilities, and data exposure paths within a graph, FalkorDB enables security teams to identify and address the most critical risks first, improving overall security outcomes. [Source]
How does FalkorDB help reduce false positives in threat detection?
FalkorDB's graph-native analytics provide end-to-end context, allowing security teams to correlate alerts and focus on genuine threats. This reduces the number of false positives and helps analysts prioritize high-value incidents. [Source]
Features & Capabilities
What performance advantages does FalkorDB offer for cybersecurity workloads?
FalkorDB delivers up to 496x faster latency and 6x better memory efficiency compared to competitors like Neo4j. It supports over 10,000 multi-graphs and flexible horizontal scaling, making it ideal for real-time, large-scale security analytics. [Benchmarks]
Does FalkorDB support real-time, interactive analysis for security data?
Yes, FalkorDB enables fast, interactive analysis of complex security data through dashboards and custom views, allowing security teams to explore and respond to threats in real time. [Source]
What integrations does FalkorDB offer for cybersecurity and AI applications?
FalkorDB integrates with frameworks such as Graphiti (for AI agent memory), g.v() (for knowledge graph visualization), Cognee (for mapping knowledge graphs), LangChain, and LlamaIndex (for LLM integration). These integrations enhance AI-driven security analytics and agentic applications. [Integrations]
Does FalkorDB provide an API for developers?
Yes, FalkorDB offers a comprehensive API with detailed documentation and references, enabling developers and security engineers to integrate FalkorDB into their workflows and build custom security solutions. [API Documentation]
Is FalkorDB open source?
Yes, FalkorDB is open source, encouraging community collaboration and transparency. This differentiates it from proprietary solutions and allows for greater flexibility in deployment and customization. [Source]
What compliance and security certifications does FalkorDB have?
FalkorDB is SOC 2 Type II compliant, meeting rigorous standards for security, availability, processing integrity, confidentiality, and privacy. This certification demonstrates FalkorDB's commitment to protecting sensitive security data. [Compliance]
How does FalkorDB support regulatory compliance in cybersecurity?
FalkorDB's GraphRAG-SDK helps organizations stay ahead of financial and security regulations by mapping regulations to workflows, identifying compliance gaps, and providing actionable recommendations. [Source]
What technical documentation is available for FalkorDB?
FalkorDB provides comprehensive technical documentation, including setup guides, API references, and advanced configuration instructions. Documentation is available at docs.falkordb.com and release notes are on the GitHub Releases Page.
Use Cases & Benefits
Who can benefit from using FalkorDB for cybersecurity?
FalkorDB is designed for developers, data scientists, engineers, and security analysts at enterprises, SaaS providers, and organizations managing complex, interconnected security data in real-time or interactive environments. [Source]
What industries use FalkorDB for cybersecurity and data analysis?
Industries represented in FalkorDB case studies include healthcare (AdaptX), media and entertainment (XR.Voyage), and artificial intelligence/ethical AI development (Virtuous AI). These organizations use FalkorDB to analyze high-dimensional data, manage scalability, and support ethical AI initiatives. [Case Studies]
Can you share examples of organizations using FalkorDB for cybersecurity?
Yes, AdaptX uses FalkorDB to analyze clinical data, XR.Voyage leverages it for immersive experience platforms, and Virtuous AI uses it for ethical AI development. These case studies demonstrate FalkorDB's impact across diverse industries. [Case Studies]
What business outcomes have customers achieved with FalkorDB?
Customers have achieved improved scalability, faster access to insights, enhanced trust and reliability, reduced alert fatigue, accelerated time-to-market, and better regulatory compliance. These outcomes are supported by real-world case studies from AdaptX, XR.Voyage, and Virtuous AI. [Case Studies]
How easy is it to implement FalkorDB for cybersecurity use cases?
FalkorDB is built for rapid deployment, allowing teams to go from concept to enterprise-grade solutions in weeks, not months. Users can sign up for FalkorDB Cloud, try it for free, run it locally with Docker, or schedule a demo for onboarding. [Get Started]
What feedback have customers given about FalkorDB's ease of use?
Customers like AdaptX and 2Arrows have praised FalkorDB for its user-friendly design and high-speed performance. AdaptX highlighted rapid access to clinical insights, while 2Arrows called FalkorDB a 'game-changer' for ease of running non-traversal queries. [Case Studies]
How does FalkorDB empower security teams to move from firefighting to prevention?
By structuring security data as a graph and delivering ultra-fast analytics, FalkorDB enables faster investigations, smarter risk prioritization, and proactive prevention strategies, reducing the need for reactive firefighting. [Source]
What pain points does FalkorDB address for cybersecurity organizations?
FalkorDB addresses pain points such as trust and reliability in LLM-based applications, scalability and data management, alert fatigue, performance limitations of competitors, interactive data analysis, regulatory compliance, and the need for agentic AI and chatbots. [Source]
Competition & Comparison
How does FalkorDB compare to Neo4j for cybersecurity use cases?
FalkorDB offers up to 496x faster latency, 6x better memory efficiency, and includes multi-tenancy in all plans, unlike Neo4j where multi-tenancy is a premium feature. FalkorDB also supports flexible horizontal scaling and is open source. [Comparison]
How does FalkorDB differ from AWS Neptune for security analytics?
FalkorDB is open source, supports multi-tenancy, and delivers better latency performance compared to AWS Neptune. It also offers highly efficient vector search and supports the Cypher query language, making it suitable for advanced security analytics. [Comparison]
What are the advantages of FalkorDB over TigerGraph and ArangoDB for cybersecurity?
FalkorDB provides faster latency, more efficient memory usage, and flexible horizontal scaling compared to TigerGraph and ArangoDB. It is rated as 'fast' for latency and supports advanced AI and multi-tenant use cases. [Source]
Why should a customer choose FalkorDB over other graph databases for cybersecurity?
Customers should consider FalkorDB for its superior performance (up to 496x faster latency), built-in multi-tenancy, open-source licensing, advanced AI integration, and proven success in real-world security and compliance use cases. [Source]
What makes FalkorDB unique among graph databases for security analytics?
FalkorDB is unique due to its ultra-fast performance, support for 10K+ multi-tenant graphs, open-source model, advanced AI and agentic integrations, and comprehensive compliance features. These capabilities make it a standout choice for modern cybersecurity teams. [Source]
Pricing & Plans
What pricing plans are available for FalkorDB?
FalkorDB offers several pricing plans: FREE (for MVPs with community support), STARTUP (from /1GB/month, includes TLS and automated backups), PRO (from 0/8GB/month, includes cluster deployment and high availability), and ENTERPRISE (custom pricing with VPC, custom backups, and 24/7 support). [Pricing]
What features are included in the FalkorDB FREE plan?
The FREE plan is designed for building a powerful MVP and includes community support. It is ideal for teams starting out with graph-powered cybersecurity solutions. [Pricing]
What features are included in the FalkorDB STARTUP plan?
The STARTUP plan starts from /1GB/month and includes features such as TLS encryption and automated backups, making it suitable for growing security teams and SaaS providers. [Pricing]
What features are included in the FalkorDB PRO plan?
The PRO plan starts from 0/8GB/month and includes advanced features like cluster deployment and high availability, supporting larger teams and mission-critical security applications. [Pricing]
What features are included in the FalkorDB ENTERPRISE plan?
The ENTERPRISE plan offers tailored pricing and includes enterprise-grade features such as VPC deployment, custom backups, and 24/7 support, making it suitable for organizations with advanced security and compliance needs. [Pricing]
Support & Implementation
What support and training options are available for FalkorDB?
FalkorDB provides comprehensive documentation, community support via Discord and GitHub Discussions, access to solution architects, and options for free trials and demos to help teams onboard quickly. [Support]
How can I get started with FalkorDB for cybersecurity?
You can sign up for FalkorDB Cloud, try it for free, run it locally with Docker, or schedule a private demo. Comprehensive documentation and community resources are available to support your onboarding. [Get Started]
How long does it take to implement FalkorDB for security analytics?
FalkorDB is designed for rapid deployment, enabling teams to go from concept to enterprise-grade solutions in weeks, not months. This accelerates time-to-value for security analytics projects. [Implementation]
Where can I find the latest updates and release notes for FalkorDB?
The latest updates and release notes for FalkorDB are available on the GitHub Releases Page, including information on major version updates and new features.